Many of you have probably heard of Agbogbloshie, the biggest and most infamous e-waste dump in the world. That’s where most of the “Western” world’s electronics is (illegally) sent to rest and be dismantled by young people who ruin their health breathing toxic fumes and trying to salvage the precious metals our trash contains.
But our old bits and pieces of hardware don’t just contain copper and gold, they also hold personal, corporate and military information that can be retrieved and used by cyber criminals.

KairUs art collective Linda Kronman and Andreas Zingerle
The duo KairUs (artists/researchers Linda Kronman and Andreas Zingerle) traveled to Agbogbloshie in Ghana to investigate the issue of data breaches of private information.
The result of their research is Forensic Fantasies, a trilogy of artworks that use data recovered from hard-drives dumped in Agbogbloshie to answer the question: What happens to our data when we send a computer, an hard disk or any kind of other storage device to the garbage?
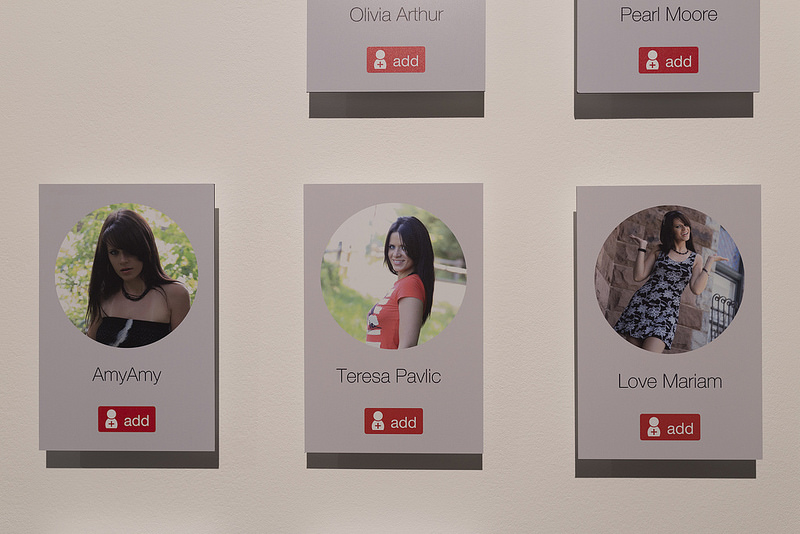
Forensic Fantasies trilogy: #2 Identity Theft, exhibited at Aksioma – Institute for Contemporary Art, Ljubljana, 2018. Photo: Janez Janša / Aksioma
The first chapter in the series, Not a Blackmail examines the possibility to identify the prior owner of a hard-drive and extort money from them (with emphasis on the word “possibility” they didn’t actually try and ransom the owner!) The second work, Identity Theft, focuses on the fraudulent online profiles created for romance scams. Finally, Found Footage Stalkers uses images retrieved from one of the hard-drives to create photo albums, as a direct reference to the traditional practice of using found footage to create new artworks.
There’s something very disturbing in Forensic Fantasies. The trilogy not only connects us with the after-life of our electronics but it also makes palpable a series of dangers that would otherwise appears far-fetched and abstract to most of us.
KairUs‘s work focuses on human computer and computer-mediated human-human interaction. Since 2010 they have investigated the issue of Internet fraud and online scams. Both of them are currently holding an Assistant Professor position at Woosong University in South Korea where they are also doing research on the vulnerabilities of Internet of Things and Smart Cities.
KairUs have an exhibition right now at Aksioma, everyone’s favourite cultural venue in Ljubljana, Slovenia. The show focuses on the Forensic Fantasies Trilogy but i’d recommend you check out the fascinating talk the duo gave at Aksioma a couple of weeks ago because it not only sums up and comment on the trilogy but also presents the artists’ ongoing research into the weaknesses and pitfalls of the much-hype Internet of Things.
Behind the Smart World: Artist talk by KairUs (Linda Kronman and Andreas Zingerle) at the Aksioma Project Space in Ljubljana on 14 February 2018
Hi Andreas and Linda! Your work Forensic Fantasies – #1: Not a Blackmail examines the possibility to blackmail the prior owner of a hard-drive. Why did you not send the hard drive back to its owner? What does the letter to the owner say?
A primary motivation to visit Agbogbloshie in the first place was to answer the questions; if it is possible to use or abuse the data on a hard-drive recovered from an e-waste dump. As we had read cases about US senators being blackmailed, company secrets exposed and recovered hard-drives from US military contractors found amongst e-waste in West Africa, we were curious if our e-waste is really such a data breach as these reports were conveying. For us, the artwork ‘Not a Blackmail’ from the ‘Forensic Fantasies’ trilogy is a proof of concept that it is possible to recover data from a hard-drive and with the help of social media profiles track current contact information of the former owner, so that this person can be contacted and then potentially blackmailed. Of course our intention was not to blackmail this person, which is made clear in the title of the artwork (‘Not a Blackmail’).
The whole Forensic Fantasies series is also about the idea of finding something sensitive or valuable on the hard-drives, and until one recovers the data there is always a chance, a fantasy of recollecting something important or of value, even scandalous. Much of the data we recovered and processed would be more or less boring for most of us in an other context, on the other hand the content of a hard-drive might still feel very personal and exposing for its former owner, so how important is it to expose this person? The name of the former owner is exposed through the artwork, but it is still common enough, avoiding a direct link to an individual. Keeping this in mind we have been thinking of ways to deliver the data back to the former owner in a way or another. Just sending the package might evoke a reaction to ignore us, so we are still waiting for opportunities to do it in a more personal way. As the artwork is still exhibited in this speculative format, we also have to think how it will be affected, how the art work changes if we actually manage to deliver the data to the owner.
The letter to the owner basically covers the story how we got our hands on his data, that we found personal and sensitive data on it that a criminal might use against him and that we decided to return the hard-drive to him.

Forensic Fantasies trilogy: #1 ‘Not a blackmail, exhibited at Aksioma – Institute for Contemporary Art, Ljubljana, 2018. Photo: Janez Janša / Aksioma

Forensic Fantasies trilogy: #1 ‘Not a blackmail, exhibited at Aksioma – Institute for Contemporary Art, Ljubljana, 2018. Photo: Janez Janša / Aksioma

Forensic Fantasies trilogy: #1 ‘Not a blackmail, exhibited at Aksioma – Institute for Contemporary Art, Ljubljana, 2018. Photo: Jure Goršič / Aksioma
One of the issues the trilogy revealed is the peril of not cleaning up or destroying hard drive before getting rid of it. How easy or difficult is it to do so exactly?
To physically destroy a hard-drive is the most secure way of getting rid of the data. There are hard-drive shredders or just drilling holes in the hard-drive is a common practice of companies, that are more aware of leaking data and want to prevent data breaches. One can also open the hard-drive and scratch the disc that contains data.
Of course if you ever saved anything in the cloud your data will be saved on hard-drives somewhere else, often copied on several locations. You will never have access to destroy these hard-drives, so we can only trust that companies have proper workflows of re-using and destroying hard-drives (this aspect also made us more aware of the materiality of the cloud).
Deleting data and emptying the virtual trash bin still allows data recovery. As long as data has not been overwritten by new data at least one time it is quite easy to recover, though recovered data is not organized which makes it more difficult to process. If a hard-drive is meant for re-use experts recommend to overwrite the data several times.
Data forensics have been able to recover data or parts of data in cases that seemed impossible such as broken hard-drives or discs destroyed by water. Yet this type of data rescue is time-consuming, needs special equipment and is expensive, whereas we were more interested in how easy it is to recover data and if data mining with very simple tools is possible at an e-waste dump.

Acquiring hard drives on the e-waste dump. Photo: Kairus.org
Could you tell us about people you met in Ghana who are also very concerned about the topics you are investigating?
What took us to Ghana in the first place is that we have been investigating internet fraud for a longer time in several of our artworks. West Africa is known for certain types of scams, but internet fraud, internet crime and scams in general are a global phenomena. People in Ghana are in general worried how trustworthy they are perceived online. Due to this bad reputation of a few scammers, service providers use the easiest way of dealing with this issue, blocking the IP-range of a whole country to access their webpage. Hence the general population is punished with quite insufficient means because with a bit of advanced knowledge this will not stop a scammer. We talked about this with several people we meet and also internet scam issues are discussed through popular culture, mainly so-called Nollywood films, that are mostly Nigerian and Ghanaian low budget films.
This perspective we try to bring forth in the second part of the trilogy ‘ID theft’ by compiling a found footage film from several Nollywood films dealing with this issue. These films are distributed as DVD’s everywhere in Ghana and are considered a very important channel for West Africans to reflect upon their own culture. Through the films it was also easier for us to discuss these issues with people we met, though in Ghana the scams were often blamed to be done by Nigerians living in Ghana. At the e-waste dump no questions were asked what we want to do with the hard-drives. As far as we talked with the workers there, they salvage and sort valuable metals such as copper cables or computer parts with gold and other metals, processors, hard-drives, etc. These parts are then sold in bulk. Hard-drives are most probably bought in bulk by data rescue companies for their spare parts. In general, mining data from the e-waste dump is probably very marginal and unknown by the general public in Ghana. A bigger concern is the illegal trade of e-waste from the US and Europe that ends up in West Africa.
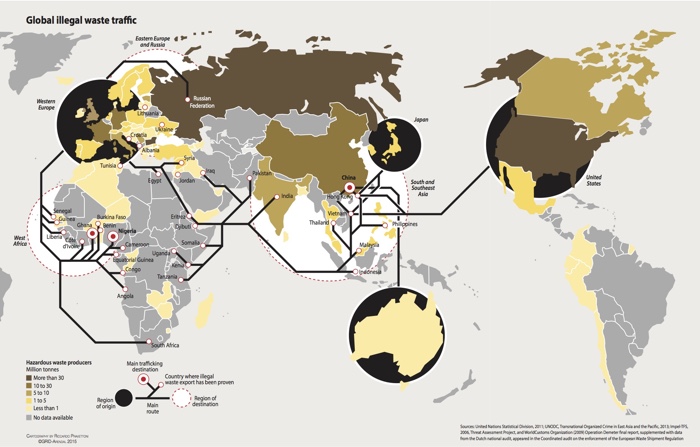
Map: Global illegal waste traffic
The work involved discussions with other artists about the ethics of using this type of ‘stolen’ material. On the one hand, people have thrown it away so it’s fair game. On the other, personal data is very sensitive. So i’m wondering what these conversations concluded about the ethic of using this data in art works? Is it just a big no no or are there conditions that make it acceptable?
Gathering and bringing back the hard-drives from Ghana was one thing, but what do you do with it and how to share it with other artists? Together with the Linz-based net culture hub servus.at we organized an artlab where we invited individuals from a trusted network of EU-based artists to participate in the project. We met in Linz for the “Behind the smart world” research lab, spending together several days to have a look at the data and give time to people to discuss and find ways to work with it.
A central issue was the privacy of the former owners of the hard-drives. Together we found different aspects on the hard-drives interesting and also developed strategies to abstract the data through artistic processes. Experiments were done to sonify folder structures, record booting attempts of the disks themselves, collages of browser cache or ascii renderings of videos and images. There was also participants attending the artlab that decided not to work with the material feeling that they had to compromise their working ethics or concerned that their reputation in handling sensitive material trusted to them would be compromised in the future. We highly respected these individual decisions.
Working with this material the longest we decided to take a more provocative approach in our third artwork Found footage stalkers we unveil the photos from one of the hard-drives, giving very personal insights into the life and habits of its former owners. Flipping trough the photos from parties with friends, trips to amusement parks and Christmas celebrations with the family evoke a similar feeling to stalking someone unknown on social media. Despite the rather uninteresting photo material, one starts to create a story and attach a personality to these fragmented digital representations. By presenting the photos in albums we approach the material as ‘found footage’, the practice of gathering material from thrift shops, yard sales and flea markets for remixing and creating new artworks, something artist have done for generations. Hence the artwork confronts earlier practices of using ‘found footage’ with now digital materials found amongst our trash. In the end, everyone has to decide for themselves how to deal with the data and what do with it. Artworks using the data from the Agbogbloshie hard-drives were shown for the first time in the ‘Behind the Smart World’ exhibition at the Art meets radical openness (AMRO) festival.

Artlab at servus.at in Linz, Austria. Photo: Kairus.org

Artlab at servus.at in Linz, Austria. Photo: Kairus.org

Forensic Fantasies trilogy: #3 Found footage stalker, exhibited at Aksioma Project Space. Photo: Janez Janša / Aksioma
Your ongoing research in South Korea, titled The Internet of Other People’s Things is, i think, a very relevant and important one because it lays bare the pitfalls of the internet of things, especially when deployed on the scale of a whole city like Songdo. How much awareness is there of that problem in Europe, among city developers, members of the public, tech companies, etc?
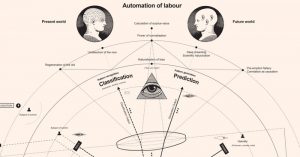
South Korea is one of the rapidly developing, tech-driven Asian states, with the second fastest and most connected society in the world, when you look at average internet connection speed and active social media penetration. At the same time, it’s a very young democracy, everything is driven by the government and market with a top-down approach, not focussing on the people who shall live in smart cities or use IoT devices on a daily basis. Cities like Songdo are built from scratch, supported by big tech companies amongst others IBM, CISCO and LG. This hyper-connected urban environments path the way to technocratic governance and city development, corporatization of city governance, technological lock-ins and hackable ‘pan-optic’ cities.
In Europe on the other hand, we see a much more inclusive development where citizens and communities become a vital part of city developments. Citizens are the ultimate actuators of a city. How are citizens involved in co-design collaborations with private corporations and the public sector to build better cities? Around this topics we are working on a publication where we seek submissions from researchers, artists, hackers, makers, activists, developers, and designers that explore vulnerabilities in IoT devices and other embedded systems e.g. in smart cities. We aim to bring artworks, projects, and essays together to create new critical perspectives on ubiquitous technologies. The full open call can be found on our website.

A view over the ‘central park’ of Songdo. Photo: Kairus.org

Not functioning automated vacuum waste collection system in Songdo. Photo: Kairus.org
Could you give a few example of the dangers you see in this massive investment in building ‘smart’ cities out of scratch and implementing IoT in our cities and homes? Do you think it is doomed to fail and be hacked or are there better ways to implement IoT?
Well, there is a couple of thing we were able to observe.
One is what we call the ‘Ruins of a smart city’. With this we imply designs, scenarios and technology that is hyped when a smart city is planned, yet already obsolete or even dysfunctional in the process of building the city. For example in Songdo City there is a central pneumatic waste disposal system. Citizens can activate a smart trash bin with their ID cards and are then able to deposit their garbage in the bins. The trash gets transported at high speed through underground pneumatic tubes to a collection station where it is separated and recycled. The city wants to eliminate the need for garbage pick-up. During a field research together with activists from Seoul-based Unmakelab, we were able to observe that the trash system is not working and piles of trash become part of the urban landscape. On the other hand, residents living in the buildings, that have invested in this infrastructure, now pay for a dysfunctional system.
Due to examples like this, Songdo has been criticized to be a prototype city or a test bed of technologies. For us, this shows that from a citizen perspective important questions to ask are actually maintenance, openness and sustainability of the technology one is intended to live with. The technological development progresses so rapidly and specially from a city planning perspective where 5-10 years later, many ideas they had envisioned for Songdo are unpractical or not used by the citizens.
A system that is praised in the advertisement material of Songdo is that each home is equipped with multiple screens that allows telepresence with other homes or institutions such as hospitals or schools. This is an idea developed before the times of mobile internet usage, which city really needs a stationary video telepresence infrastructure now? Other observations were non-functioning sensors paved into the streets and lamp posts. We documented this failed implementations also to point out the materiality of the “smart technologies” in a city.
Another thing we have became aware of is that through these massive smart city projects the city is increasingly being corporatized. Songdo is owned by three companies Gale International, Posco and Morgan Stanley. Further on cities naturally make contracts with technology companies who also end up owning wast amounts of citizen data.
We want to understand what kind challenges emerges when technotopian cities are not populated with their imagined tech-savvy international citizens. Who is included, who is excluded when we talk about smart cities? On the other hand, how do actual residents reshape, redesign, misuse or opt out from technological lock-ins?
Until now we have been mostly concentrating on Songdo which is categorized as a first generation smart city, followed by several generations that gradually starts to consider the citizen also in planning. Also the term ‘smart city’ has been widely contested while it represents diverse values, solutions and implementations depending on context.
Further on when we investigate ‘smart cities’ we are looking at those current and future scenarios in which our things are wirelessly connected, so Internet of Things. We do not think that IoT is doomed, but we see that designs are far from being sustainable, privacy respecting and somewhat secure. We are not against the development of IoT per se, though we are also not convinced that the proposed technologies that are branded ‘smart’ are best practices of solving the problems they intend to tackle.

Panopticity: ‘Seoul’ video screenshot. Photo: Kairus.org
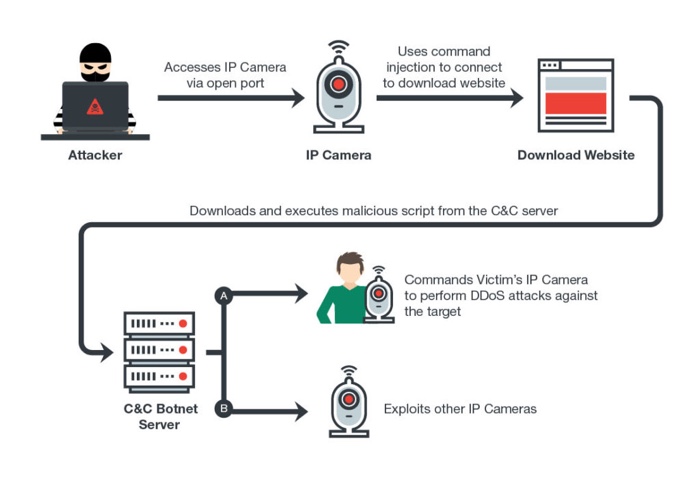
How an attacker runs DDoS attacks on a victim’s IP camera
Could you explain the first work you did in that research, the city portrait of Seoul through insecure public CCTV and private IP cameras?
Cities, companies and private persons use networked security cameras often including tracking software for their surveillance. Various brands offer products with integrated web-server allowing remote processing and streaming of the video footage, adding these devises to the growing amount of connected devices. These web-servers are often ‘insecure by design’, meaning they are not protected by a password or have hard-coded login credentials saved as plain text. By default, the servers stream unencrypted and on publicly-accessible network ports, providing potential risks of being intercepted and allowing unknown third parties unintended access to the set up function of the cameras. Some manufacturers use the same vulnerable settings across their entire camera lineup.
“By default, the Network Camera is not password-protected”, or “the default user name is admin” and “the password is 12345” can be read in the camera manuals. We recorded video footage from these web streams and assembled it into a city portrait through the lenses of unsecured video cameras. The experimental video is currently touring film festivals and we are finishing a video installation that portrays mega-cities around the world through their unsecured video cameras. Paradoxically the security camera becomes a security risk. We are also fascinated to see what is surveilled around the world in the name of security.

KairUs, Forensic Fantasies. Artists talk at Aksioma – Institute for Contemporary Art, Ljubljana, 2018. Photo: Jure Goršič / Aksioma
This is probably a stupid question but i have to ask it: why are you called KairUs?
Back in 2010 when we started our artistic collaboration we were clear that we want to work with time-based interactive installation art. We adapted the ancient greek word ‘Kairos’ (καιρός) meaning the right, critical, or opportune moment. Whereas the western definition of time ‘chronos’ is purely quantitative, kairos has a qualitative, permanent nature. As artists we look for these opportune moments for our artistic expression, it encourages creativity, to adapt to unforeseen obstacles and opinions that can alter opportune or appropriate moments to produce art.
Thanks Linda and Andreas!
KairUs (Linda Kronman and Andreas Zingerle)’s solo exhibition Forensic Fantasies is at Aksioma | Project Space in Ljubljana until 16 March 2018.
And should you be a researcher, artist, hacker, maker, activist, developers or designer whose work and/or writing explores the vulnerabilities in IoT devices and other embedded systems, then have a look at this open call for submissions (deadline is 30 April 2018.)
Related stories: Permanent Error, e-waste, porn, ecology & warfare. An interview with Dani Ploeger, When erased data come back to haunt you and Harvesting the Rare Earth.