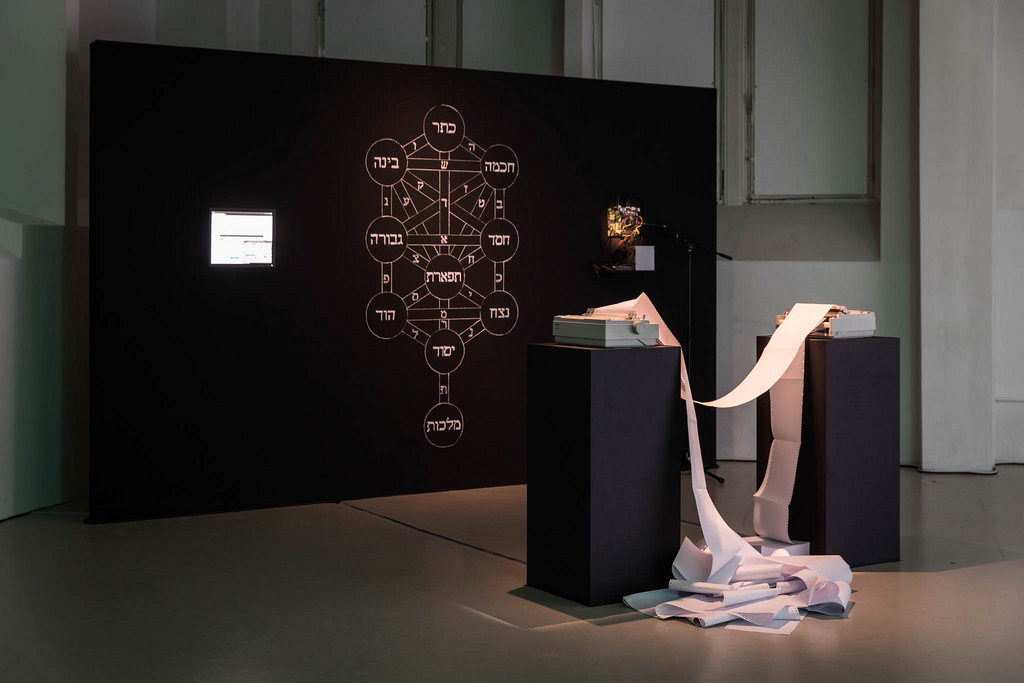
RYBN, Dataghost 2, 2016. Installation view at STUK in Leuven for the Artefact festival. Photo © Kristof Vrancken
As early as the 1st century, Jews believed that the Torah and other key religious texts contained encoded truths and hidden meanings. They used a system called Gematria to uncover them. According to this numerological system, each Hebrew letter also corresponds to a number (for example, 1 is Aleph, 2 is Bet, 3 is Gimel, 4 is Daleth, etc.) Kabbalists extended the method to other texts and, by converting letters to numbers, they looked for a hidden meaning in each word. Other hermeneutic techniques used by the Kabbalah are Temurah, which rearrange words and sentences to deduce deeper spiritual meanings, and Notarikon which creates words from letters taken from the beginning, middle, or end of words.

RYBN, Dataghost 2, 2016. Installation view at STUK in Leuven for the Artefact festival. Photo © Kristof Vrancken
RYBN, Dataghost 2, 2016. Installation view at STUK in Leuven for the Artefact festival. Photo © Kristof Vrancken
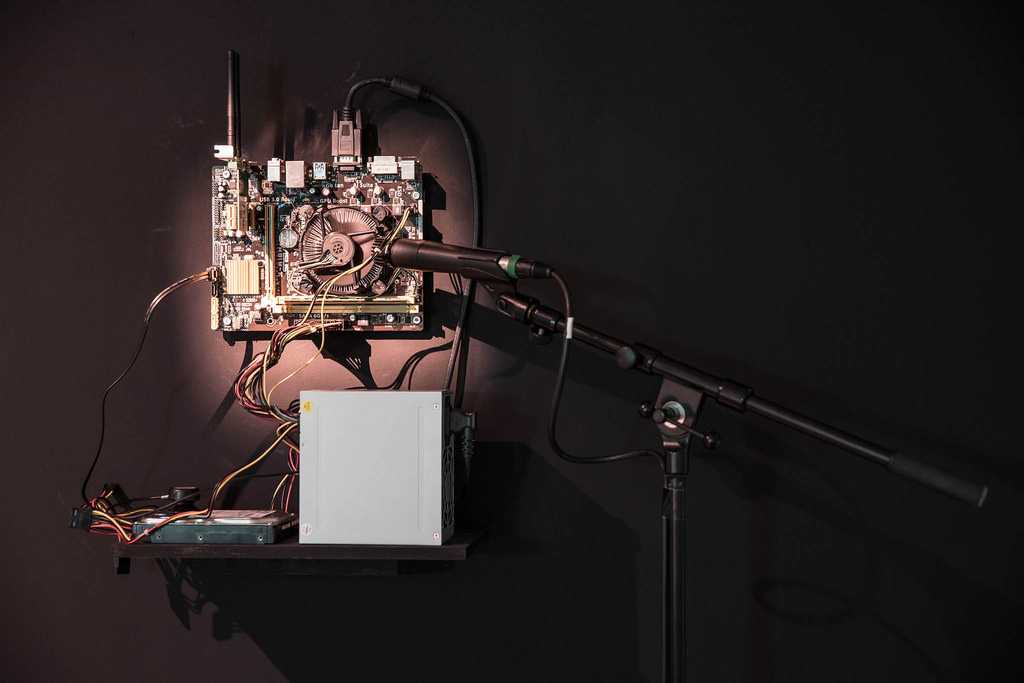
The French collective RYBN.org has applied this numerological system of transformations, associations and substitutions to computing. Their Dataghost 2 installation is a kabbalistic computational machine that seeks to reveal the hidden messages buried within the data traffic.
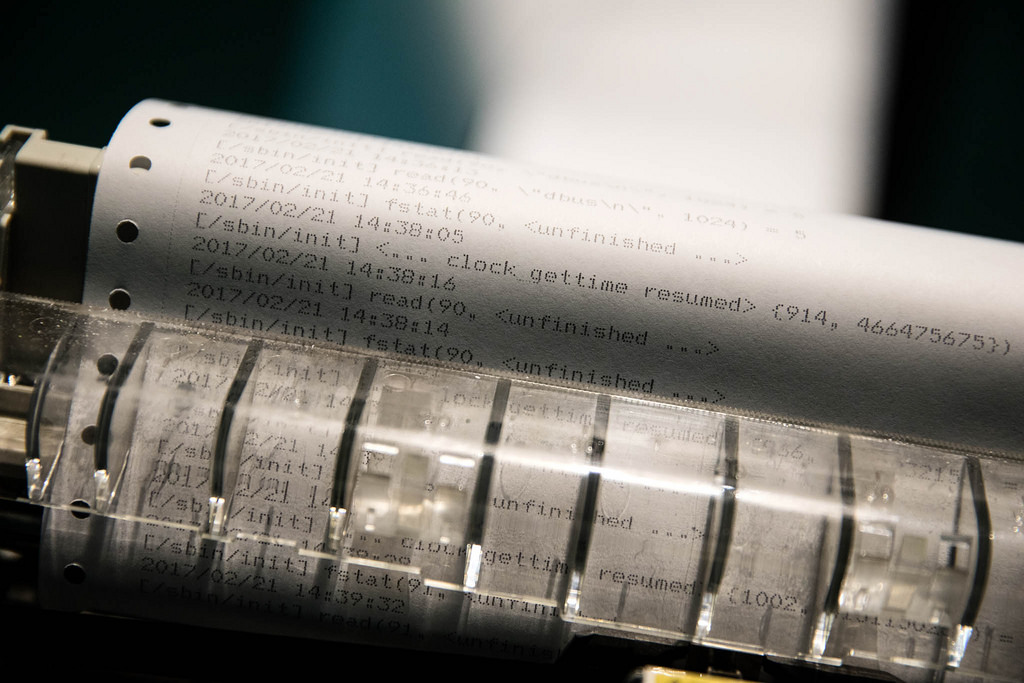
A daemon, installed on a server, catches all incoming and outgoing digital communications, and dumps their content using network interception tools. All the encapsulated data are then submitted to several decyphering algorithms, reproducing the hermeneutic techniques of Kabbalah. The raw data are decomposed and recomposed according to the substitution principles that govern the Kabbalah, in order to unveil the mystic of network communications.
By following the kabbalistic alpha-numerical system, the fragments of codes generate in the process millions of shell commands, most of them incoherent or nonfunctional. However, from time to time, the commands will ‘make sense’ to the computer. The machine will interpret them as tasks that need to be executed. At this precise moment, the machine achieves the invocation ritual of a digital Golem.
However, there is no way to predict where the ritual might lead the machine: the executed commands might saturate the memory capacity of the machine, provoke a definitive stop within the software layer, or overpass several critical limits that result in an overheating of certain electronic components, or lead to the destruction of parts of its physical layers. Over the course of its life, the system constantly publishes its self-destructive activity in the form of a printout of all the different commands.
I discovered the work two days ago at the Artefact festival at STUK in Leuven (a mere 15 minute away from Brussels so take the train now if you’re in Belgium because the show is as enchanting as its theme suggests) and Dataghost 2 was dead. The demise came quite early. The email exchange in which the artists and STUK tried to understand what had happened was printed out and added to the exhibition space. The emails reveal that the system probably erased a critical file which brought the whole process to its term.
The installation is currently running in dead mode. Both the printing machine and the screen remain frozen.
RYBN, Dataghost 2, 2016. Installation view at STUK in Leuven for the Artefact festival. Photo © Kristof Vrancken

RYBN, Dataghost 2, 2016. Installation view at STUK in Leuven for the Artefact festival. Photo © Kristof Vrancken
I found the work brilliant. On the one hand, it is super complex and perplexing, just like most esoteric practices. On the other hand, it demonstrates with great efficiency and simplicity that algorithms (and by extension any technology system) are only as rational (or irrational) as the humans who program them.
Dataghost 2 is exhibited at the Artefact : The Act of Magic in Leuven, Belgium. The exhibition, curated by Karen Verschooren from STUK & Ils Huygens from Z33, continues until 9 March 2017.
If you find yourself in Paris, the RYBN collective will be discussing Dataghost 2 tomorrow 3 March at the Ecole Nationale Supérieure d’Arts de Paris Cergy.
Related stories: The Occult, Witchcraft & Magic. An Illustrated History.