Paul Timmins, a Michigan men of 23, pleaded guilty of unauthorized access to a protected computer.
Together with Adam Botbyl, now 21, he stumbled across the unsecured wireless network at the Southfield, Michigan Lowe’s in the spring of 2003, while driving around with laptops looking for wireless networks.
Timmins used the network to check his email, but when he wanted to surf the Web as well, he realized it was a private corporate network, and disconnected.
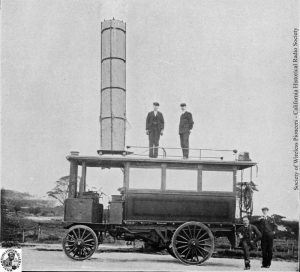
![rig14[1].jpg](http://www.we-make-money-not-art.com/xxx/rig14%5B1%5D.jpg)
Botbyl noted the network, and six months later returned with his friend Brian Salcedo, a 21 year-old hacker, to route through the company’s corporate data center and connect to the local networks at stores in Kansas, North Carolina, Kentucky, South Dakota, Florida, and two stores in California.
At two of the stores, they modified a proprietary piece of software that Lowe’s uses to process credit card transactions, and built in a wiretap to store customer’s credit card numbers and retrieve them later.
Lowe detected the intrusions, and called in the FBI which spotted the duo out the Southfield Lowe’s parking lot, followed them, and found the bugged program, which had collected six credit card numbers.
All three men were charged with computer intrusions, damage and fraud.
Botbyl faces 41 to 51 months in prison under federal sentencing guidelines; Salcedo faces a harsh 12 to 15 year prison term.
Timmins’ possible sentence ranges from probation, to a maximum of 12 months in custody.
Cyberlaw lawyer Jennifer Granick, agrees that Timmins’ is likely the first wardriving conviction. But she isn’t convinced that he actually committed a crime.
“Using an open wireless access point isn’t the same thing as using a computer illegally,” says Granick. “Convictions for this type of thing are possible where it’s part of a larger criminal case, but it shouldn’t happen in the absence of some other criminal purpose, like stealing credit cards, or knowledge that the network is closed. Wardriving isn’t criminal.”
From The Register.